Web3Auth Shamir Secret Sharing Architecture
This document provides an in-depth exploration of the technical architecture of the Shamir's Secret Sharing (SSS)-based SDKs, this includes the current Plug and Play and Single Factor Auth Mobile SDKs.
SSS is a base form of Multi-Party Computation (MPC) that splits a secret into shares, of which threshold are required to reconstruct the secret.
Alternatively, consider the MPC architecture which does not fully-reconstruct the key.
| SDK Family | Key Model | Available from |
|---|---|---|
| Embedded Wallet SDKs | SSS (key reconstruction) | Base, Growth, and Scale plans |
| MPC Core Kit SDK | TSS/MPC (no key reconstruction) | Enterprise plan |
Components
The accompanying image illustrates the typical flow of wallet management within the SSS infrastructure.
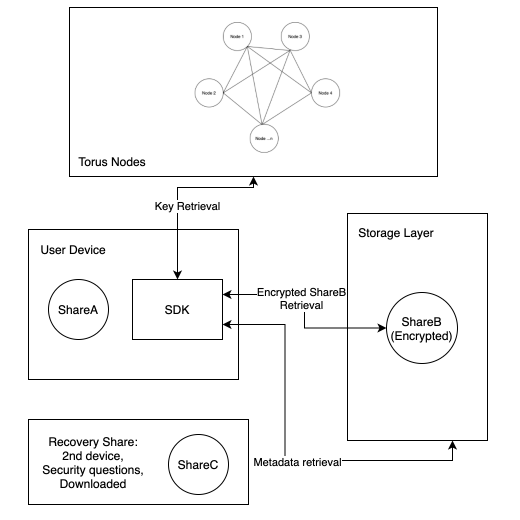
Auth nodes (enabling social login)
Auth nodes provide a user-specific key based on some form of attestation from the user. This attestation could come in the form of an OAuth login from an existing account, a traditional email account login, or even biometrics. Nodes need not return a private key, but need to fulfill the interface:
For ease of illustration the rest of this document assumes that this is implemented with secp256k1 keys and ECIES. The key retrieved from the nodes is referred to as an encryption key or .
Storage layer
The storage layer serves as a persistent data store for storing encrypted metadata. Examples of such systems include IPFS, Arweave, Sia, or even Byzantine Fault Tolerant (BFT) layers. Data availability and cost are the main factors to consider but the choice of storage layer is ultimately up to the implementer.
Our SSS infrastructure utilizes from the nodes as an entry point to retrieve the private key. is used to retrieve encrypted user-specific data from the storage layer, referred to as metadata. This data includes a user's threshold, polynomial commitments, associated devices, and so on.
User device
The SSS infrastructure is dependent on user devices to store shares. The base flow accommodates a single device, but users can use multiple devices to increase the threshold once they have an initial setup. Access to device storage on the user's device is implementation specific. For example, for native applications on mobile, they can make use of the device keychain.
Recovery share
This is generally not used during normal operation, and is intended for use in key recovery / share refresh if the user loses their device or shares.
Flows
Key handling on user login
Key handling begins in response to a user-triggered action, such as logging in. At this stage, the system attempts to retrieve any existing encrypted metadata associated with the user.
If metadata is found, the user is an existing user. The metadata is decrypted using the nodes’ , and the stored information is used to validate the user and load the existing secret-sharing parameters. No new key material is generated in this path.
If no metadata is found, the user is treated as a new user, and a new key is initialized. In this case, a 2-of-3 Shamir’s Secret Sharing (SSS) polynomial is generated, producing a private key and its corresponding shares.
We select a polynomial over where:
- denotes the private key scalar to be used by the user
- is a polynomial coefficient to
- and are ShareA, ShareB, and ShareC respectively
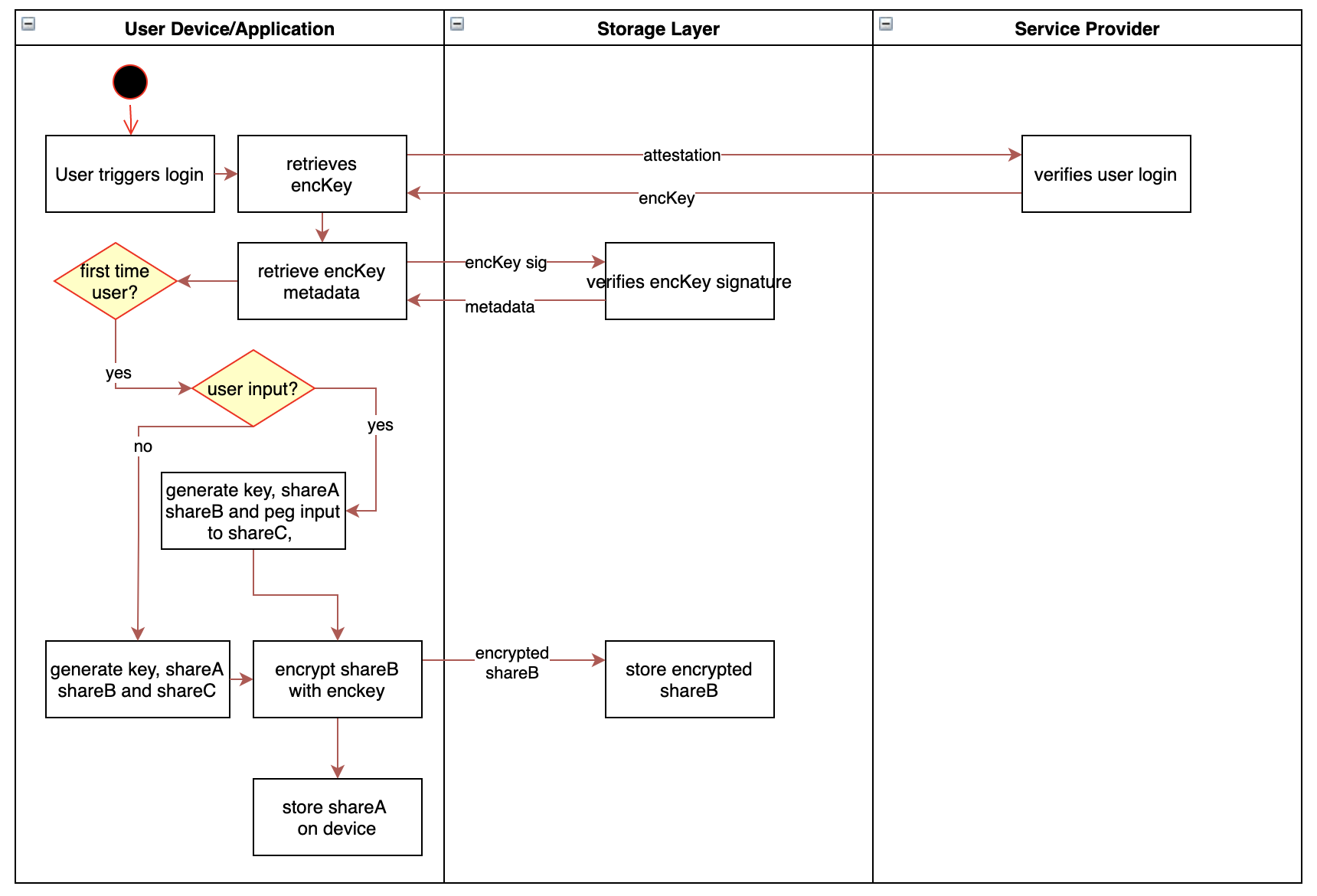
ShareA is stored on the user's device, ShareB is encrypted with the and stored on the storage layer for future retrieval, and ShareC dependent on user input or handled as a recovery share.
Key reconstruction
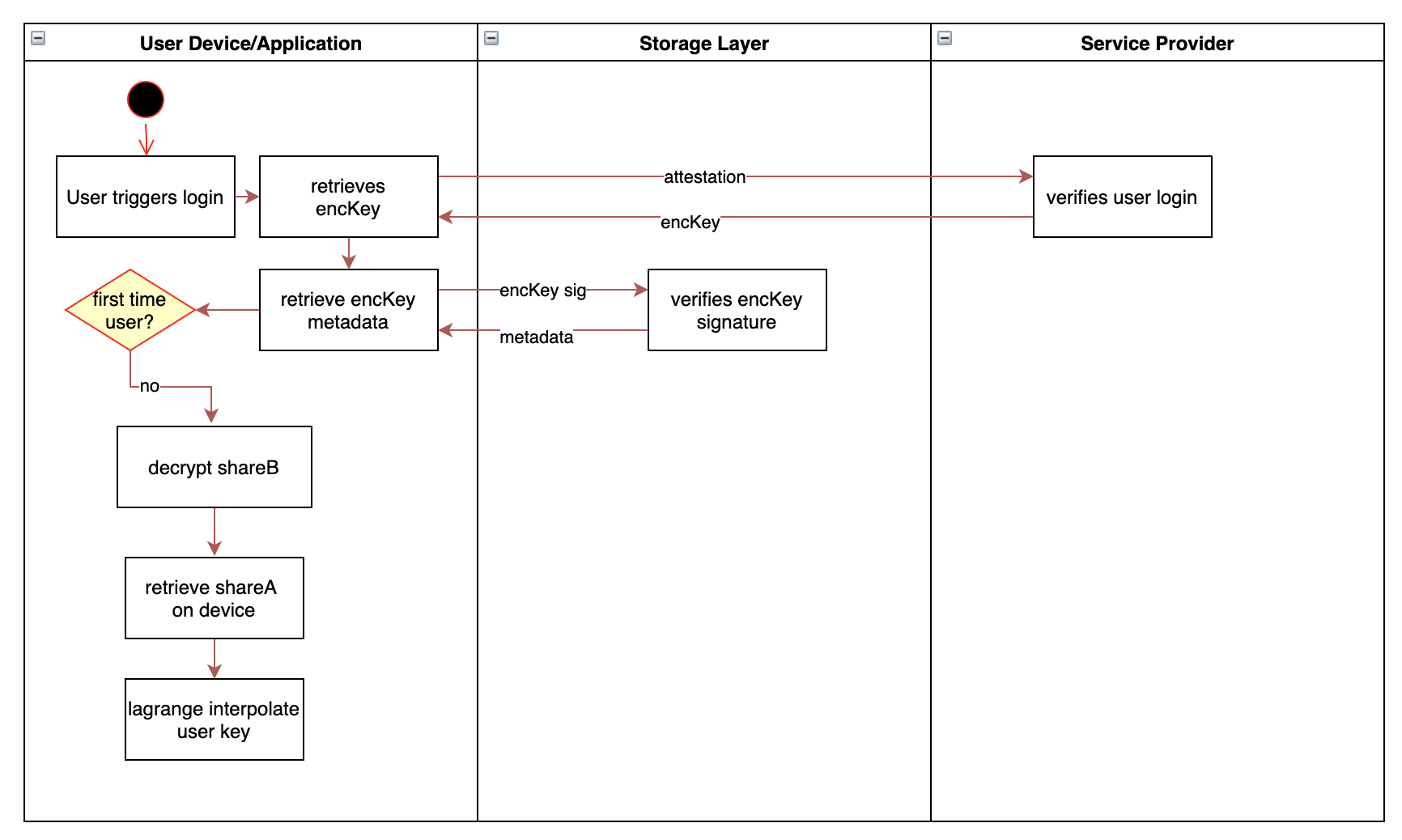
If a user has logged in previously, they reconstruct their key by decrypting ShareB (retrieved through the storage layer) and combining it with ShareA on the user's current device using Lagrange interpolation.
Key generation with deterministic share
Provided with a user input, , we can predetermine a single share in the generation of the SSS polynomial, where we peg ShareC or to a user's input. Let be a cryptographically secure hash function. Given: .
In the case of secret resharing, we can also conduct the deterministic generation of the polynomial with a given and . We are able to peg given values to the key or shares as long as where is the degree of the SSS polynomial .
It is important that has sufficient entropy in its generation. A potential way to guarantee this is via using several security questions (for example a minnimum of three) with answers to derive . This can be implemented with a repository of questions, of which order and index can be defined in metadata.
Candidate qualified questions should have deterministic answers (such as, "your parent's birthday" or "your city of birth"), rather than "what's your favorite singer?". To accommodate for cases that users tend to forget their answers, there is a further potential of splitting the answers themselves via SSS such that the user can answer 3/5 questions, giving redundancy.
Expanding the number of shares (adding a device)
In the case of adding a new device, the user needs to migrate a share to the device to reconstruct their key. This can be done via user input or through a login to a current device.
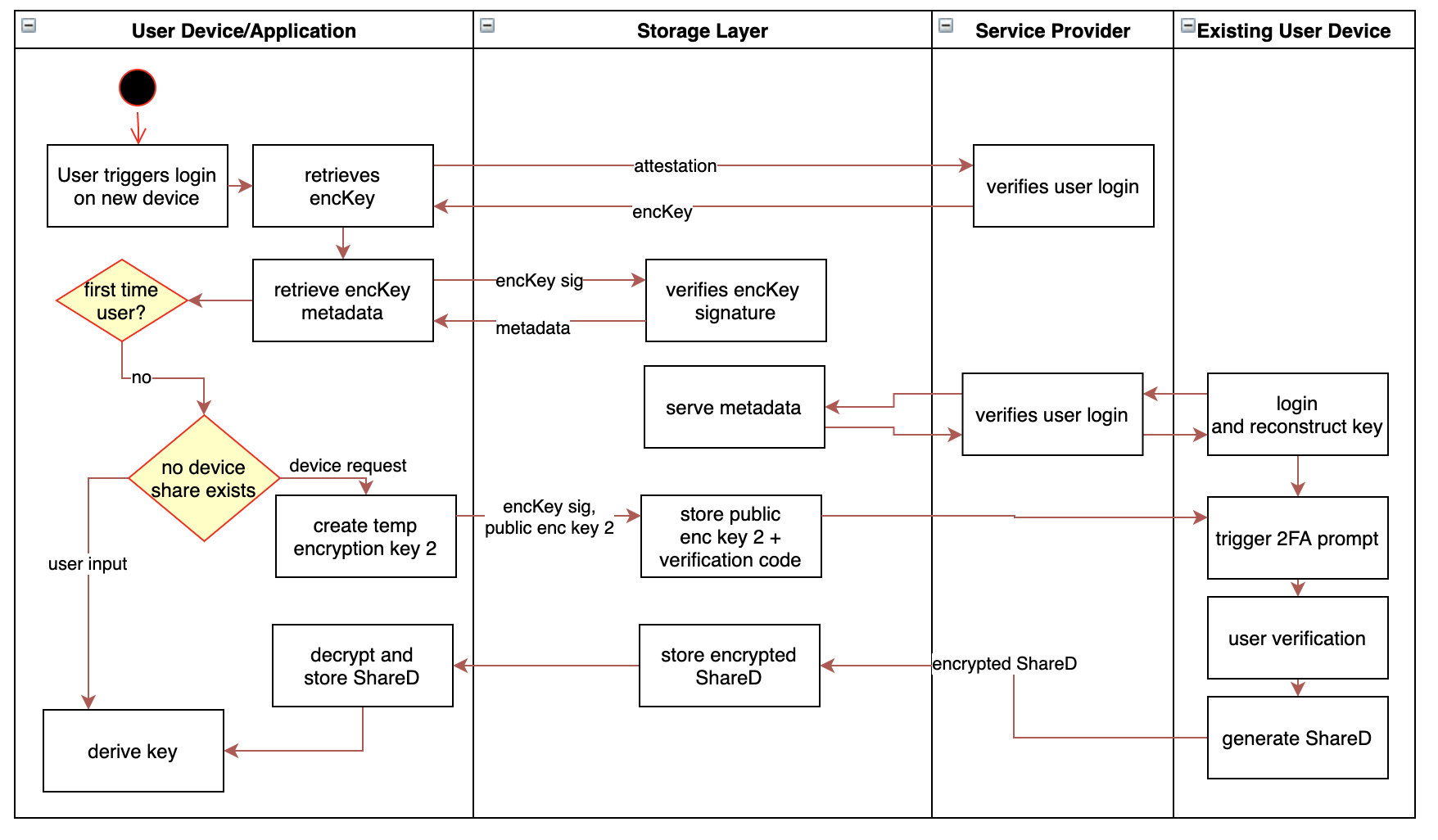
On reconstruction of on the new device, we set ShareD to .
Share resharing and revocability
Utilizing the storage layer, we are able to generate new shares for all devices, regardless if they are online or offline. This allows us to remove devices from the sharing, allow the user to change their security questions and/or adjust their security threshold. The key concept here is utilizing published share commitments as encryption keys to retrieve shares on the most updated SSS polynomial.
This is illustrated from a 2/4 SSS sharing with shares kept on 3 user devices and the nodes. Let be a generator of a multiplicative subgroup where the discrete log problem is assumed hard to solve. During initialization of the key we create share commitments to be stored on the storage layer. These share commitments are analogous to public keys derived from the share scalars.
Given the user loses device D holding , and wants to make that share redundant, they first reconstruct their key on device A. We utilize a public key-based encryption scheme (ECIES).
The user generates a new 2/3 SSS polynomial on the same with shares and encrypts the newly generated shares for each respective share commitment, except for the lost commitment.
, the resulting ciphertext from the encryption, is then stored on the storage layer for retrieval on other devices.
On login to device B, the user retrieves is able to use to decrypt the new and reconstruct their key with derived from the nodes in a similar fashion. Using the allows to also be deprecated as a share.
Resharing allows us to share a key on a new polynomial with a different degree/threshold, allowing us to also increase a user's security/factor devices or inputs to reconstruct their key as they require it. This can be incrementally done as needed.